Well, that was some challange to find it out. But as often, Powershell is your friend. With few lines of code, fully customizable, you can change the UPN for all users within an organizational unit. So you will save time, because you just have to change the OU in the script.
The change UPN script
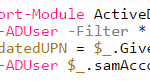
[code language=”powershell”]
Import-Module ActiveDirectory
Get-ADUser -Filter * -SearchBase "OU=lan.driftar.com Users,OU=LAB-Users,DC=lan,DC=driftar,DC=com" | ForEach {
$UpdatedUPN = $_.GivenName + "." + $_.SurName + "@driftar.com"
Set-ADUser $_.samAccountName -UserPrincipalName $UpdatedUPN
}
[/code]
What does the script?
The script searches within the organizational unit specified for the user accounts, combines givenname and surename with the domain prefix, and changes then the UPN for all the user accounts withing this organizational unit. In this example the new User Principal Name for a user will be “givenname.surename@driftar.com” (for example john.doe@driftar.com).
Conclusion
To be honest it was some time needed to search for the right script parameters and test it out, to make sure everything works. But you don’t do that every time. You can save this script and customize it every time for the customer you work for. It’s a quick way to change the UPN, and it’s an easy way to save time.